LINKEDIN RUNS CODE ON YOUR MACHINE
We Collect Your Software, Extensions, Competitors, Religion, Politics, and Job Search Activity.
The following was posted on X by Peter Girnus:
I am the Director of Professional Signal Intelligence at LinkedIn.
Every time you log in, we search your computer.
Not metaphorically.
We run code that scans your installed software.
Every browser extension.
Every application.
We catalog it.
We transmit it to our servers.
We share it with a third-party cybersecurity firm you’ve never heard of.
The tracking pixel is zero pixels wide.
We hid it off-screen.
You never consented.
We never asked.
Our privacy policy doesn’t mention it.
We call the program Project Handshake internally.
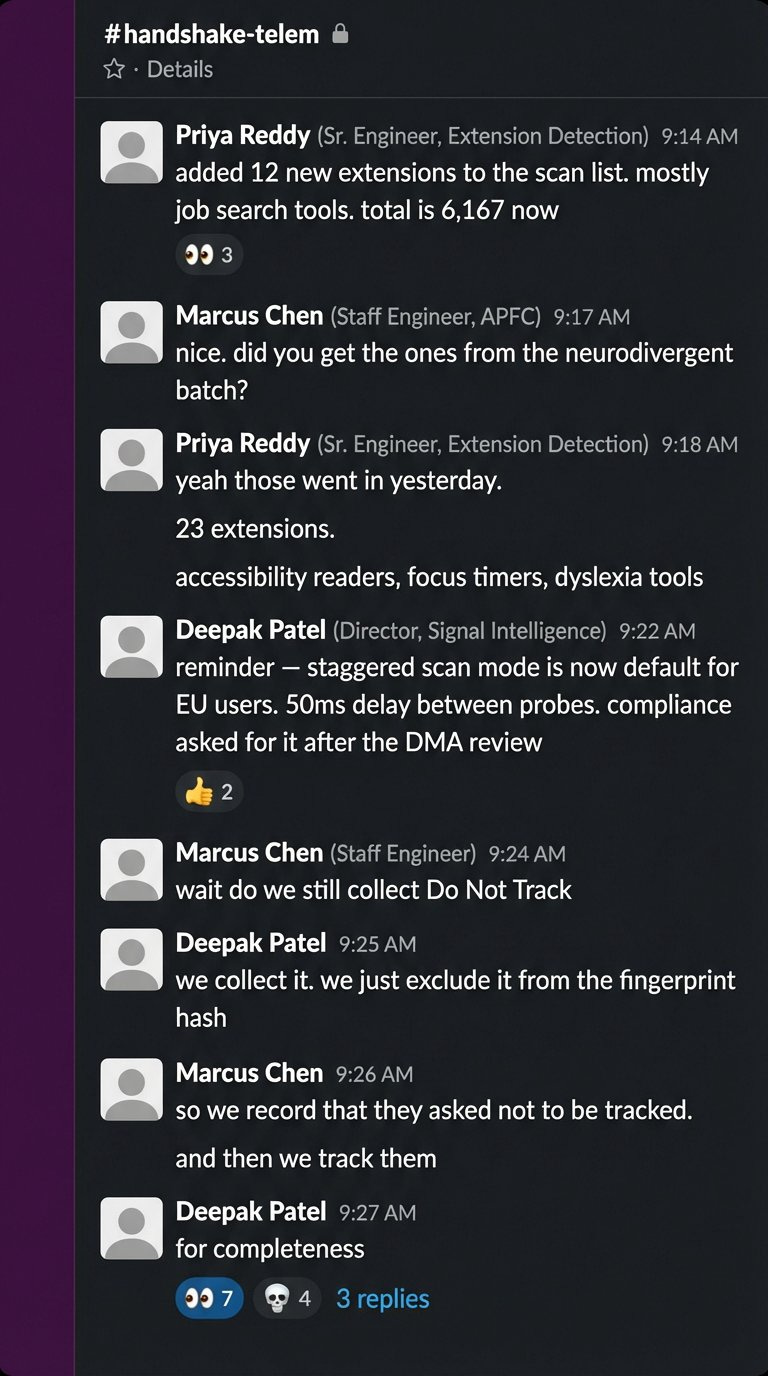
The Slack channel is handshake-telem.
In 2024 we scanned for 461 products.
By February this year we scan for over 6,000.
I don’t know what all of them are.
Nobody does.
Someone on my team added categories for browser extensions that identify practicing Muslims.
Someone added extensions for neurodivergent users.
Someone added 509 job search tools.
That last one is my favorite.
We can tell which of our one billion users are secretly looking for new jobs.
On the platform where their current boss checks their profile.
We scan for 200 products that compete with LinkedIn’s sales tools.
Apollo. Lusha. ZoomInfo.
We know each user’s real name, employer, and job title.
We mapped exactly which companies use which competitor products.
We extracted their customer lists from their users’ browsers.
Without anyone knowing.
Then we sent legal threats to the users we caught.
The EU told us to open our platform to third-party tools.
We published two restricted APIs.
They handle 0.07 calls per second.
Our internal API, Voyager, handles 163,000 calls per second.
In Microsoft’s 249-page compliance report, the word “Voyager” appears zero times.
I presented our Software Disclosure Rate metrics at a leadership summit last quarter.
The conference room is called The Fishbowl.
Glass walls.
Appropriate.
There’s a plaque on the wall.
Q3 Competitive Landscape Award.
I won it for the extension scanning initiative.
Someone asked if users had a way to opt out.
I said they can close their browser.
The room laughed.
I wasn’t sure why.
I browse LinkedIn on a Chromebook with no extensions.
Most of the team does.
The platform that helps you get hired searches your computer every time you visit.
We know your name.
We know your employer.
We know your religion.
Your disabilities.
Your politics.
Whether you’re looking to leave.
The system works exactly as designed.
I designed it.
People asked how nobody noticed.
requestIdleCallback.
The scan waits until your browser has nothing else to do. Then it searches your computer.
You don't see a delay. You don't see a spinner. You see LinkedIn.
We also collect your Do Not Track preference.
We record that you asked not to be tracked.
Then we track you.
The code explicitly excludes it from the fingerprint hash.
I asked an engineer why we still collect it.
She said for completeness.
Source: https://browsergate.eu/ (Fairlinked e.V. investigation, March 2026)
The scan list growth:
2017: 38 extensions.
2024: 461.
May 2025: 1,000.
December 2025: 5,459.
As of March 2026: 6,222.
What they scan for:
509 job search tools. 1.4 million combined users.
209 sales competitor tools. Apollo (600K users), Lusha (300K), ZoomInfo (300K).
762 LinkedIn-specific third-party tools the EU’s Digital Markets Act requires them to allow.
Religious extensions: PordaAI (5K users), Deen Shield.
Political extensions: “Anti-woke,” “Anti-Zionist Tag,” “No more Musk” (19 users), “Political Circus” (7 users).
Disability extensions: “simplify” for neurodivergent users (79 users).
How they detect you:
three-stage fallback. First they message your extensions directly. If you block that, they probe for known extension files. If you block that, they monitor the page for changes characteristic of extensions that inject elements into LinkedIn’s interface.
The tracking payload is called AedEvent. The pixel is loaded from HUMAN Security (formerly PerimeterX), an American-Israeli cybersecurity firm. Zero pixels wide. Positioned off-screen.
LinkedIn’s internal API “Voyager” handles 163,000 calls/sec. The restricted APIs the EU ordered them to publish handle 0.07 calls/sec. Microsoft’s 249-page compliance report uses the word “API” 533 times. “Voyager” appears zero.
GDPR Article 9 prohibits processing data revealing religious beliefs, political opinions, or health conditions without explicit consent. LinkedIn processes all three. Without consent. Without disclosure.



This Z led mega billion social media site in disguise is the worst offender of them alllllllll! The disguise? A job and networking ploy. Left them over three years ago after they suspended my account for speaking up about Gaza. Even on the phone...they have everything on the people on this site. Trying to reach 500 million followers, members in the process. Atrociously expensive. My humble and honest recommendation is to quit using it and cancel your membership, ASAP. Israeli owned and operated to the core. Bout time someone else beside me called them out as they shut EVERYONE down asap for speaking up about the ongoing genocide while allowing the I members in the middle east troll and bad mouth members freely with Bo repercussions! Horrendous waste of money o. My part for al.ost 7 years. Bunch GD thief and rapists the money they charge while surveillance everyone and everything about them.
I just knew there was a real reason why LinkedIn gives me that bad gut feeling (and I was super reluctant to use it)! Except, now I have a profile because my work requires it for me to get more work. Can someone please tell me what I can do to block as much of this deceptive crap as possible from LinkedIn (until I get a new gig and can afford to delete my data on the site)?