The Private Spy Industry Quietly Rewriting Democracy
A global system targeting journalists, activists, and entire populations
The Private Intelligence War: Who Controls What the World Sees
Israeli private intelligence companies and spyware firms have interfered in elections around the world, surveilled presidents and political leaders, disrupted negotiations, and contributed to environments where journalists and activists have been targeted and killed.
This is not a series of isolated incidents.
It is a system—built through long-standing relationships between former intelligence officials, private contractors, and governments—operating through contracts, partnerships, and plausible deniability.¹
According to the research group Forensic Architecture, NSO Group’s technology has been linked to more than 150 physical attacks against journalists, human rights advocates, and civil society actors, including cases resulting in death.²
This is not simply surveillance.
It has real-world consequences.
Disinformation as Infrastructure
Disinformation is no longer chaotic or decentralized. It is organized, industrialized, and sold.
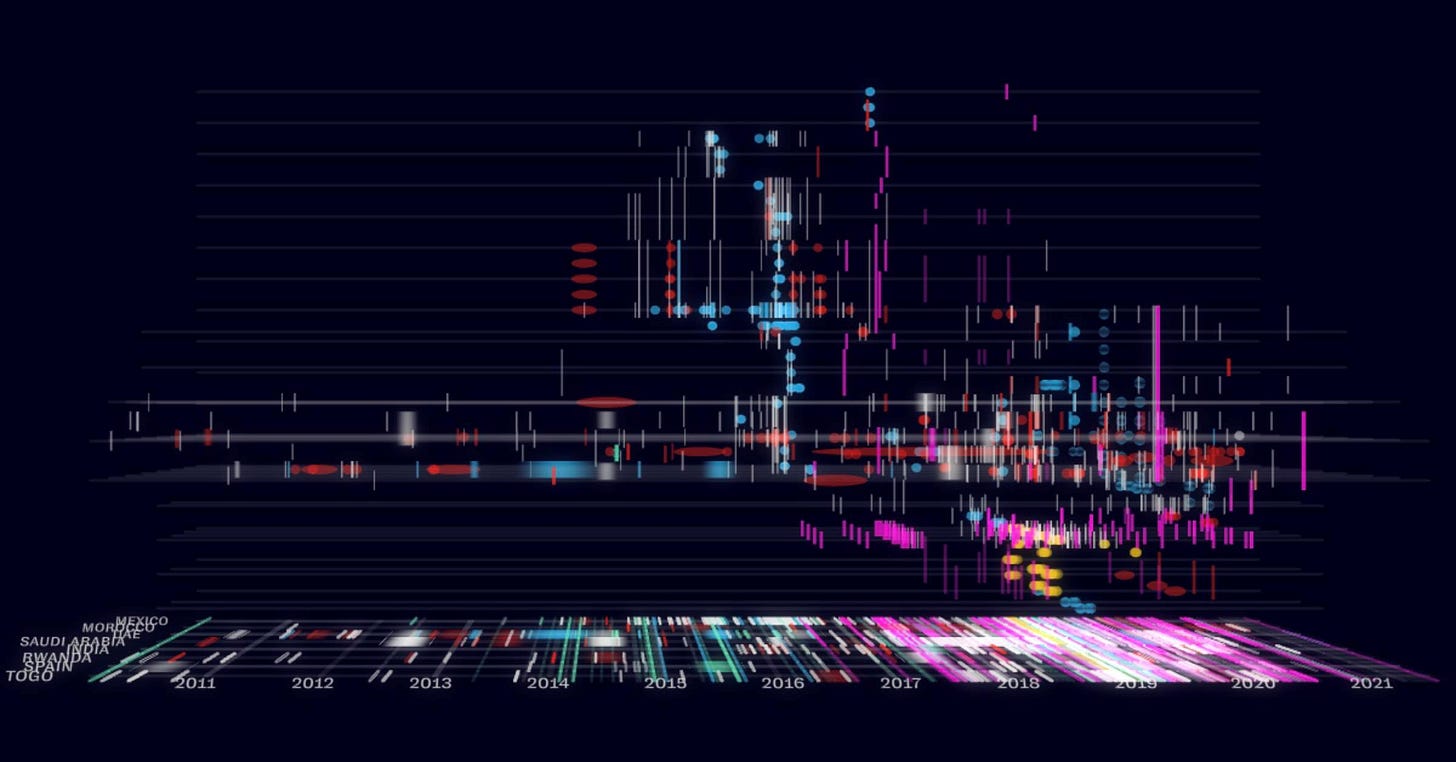
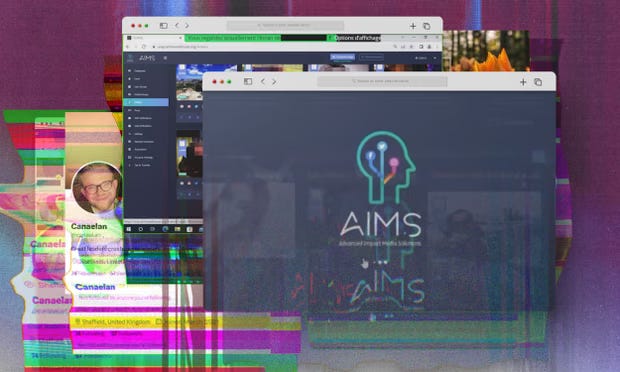
Advanced Impact Media Solutions (AIMS), operated by “Team Jorge,” controls more than 30,000 fake social media profiles, enabling large-scale narrative manipulation.³
In 2022, its operator Tal Hanan claimed involvement in 33 presidential campaigns globally—27 successful.⁴

Investigations have shown these operations include hacking, sabotage, automated disinformation, and coordinated narrative placement across platforms.⁴ ⁷
Hanan has stated that these services were offered to intelligence agencies worldwide.⁵
These tactics are not theoretical.
Ahead of U.S. elections, coordinated networks infiltrated political communities online—posing as real users and flooding them with targeted propaganda designed to distort voter perception.⁶
Some operations have been linked to Israeli firms such as Demoman International, which has appeared on infrastructure connected to Israel’s defense establishment.⁸
Investigations have also revealed the ability to place manipulated narratives directly into mainstream media channels, including television.⁹
The Industry Exists Because It’s Designed To
Private intelligence firms allow governments to operate without fingerprints.
Outsource the operation.
Deny involvement.
Plausible deniability isn’t a loophole.
It’s the business model.¹⁰
The Spyware Industry
Candiru
Candiru is an Israeli spyware company that sells surveillance tools exclusively to governments. Its software can infiltrate iPhones, Android devices, computers, and cloud systems.¹¹
Citizen Lab identified at least 100 activists, journalists, and dissidents across 10 countries targeted using Candiru spyware.¹²
The technology has been linked to attacks on critics of governments and infiltration of websites across multiple regions.¹³ ¹⁴
Reports indicate the firm has sold cyber capabilities to state actors while exploiting vulnerabilities in major operating systems.¹⁵
Further research confirms its use against individuals across Iran, Lebanon, Yemen, Turkey, the UK, and beyond.¹⁶

Government Demand and Continuity
Even when firms are exposed or sanctioned, the system continues.
U.S. agencies have reportedly used Israeli spyware despite official bans, while new firms such as Paragon have emerged to replace blacklisted providers.¹⁷ ¹⁸

Paragon has been described as capable of penetrating encrypted platforms such as WhatsApp and Signal.¹⁹ ²⁰
QuaDream and Next-Generation Tools
QuaDream developed advanced spyware using zero-click exploits—allowing devices to be compromised without any user interaction.²¹ ²²
Its tools were deployed against journalists, activists, and opposition figures across multiple countries before the company shut down amid growing scrutiny.²³
Domestic Deployment
These tools are not confined to foreign intelligence.
Israeli surveillance technologies have been deployed by law enforcement agencies, including in the United States.
Cobwebs Technologies software has been used to track individuals through phone and social media data.²⁴
It has been deployed in policing and border operations.²⁵
Meanwhile, platforms themselves have acknowledged that tens of thousands of individuals were targeted by “spy-for-hire” networks offering surveillance services to paying clients.²⁶ ²⁷
3 Israelis from Black Cube intel firm given suspended sentence in Romania.
They were accused of having created an organized crime group that in 2016 targeted Laura Kovesi, a prosecutor who at the time headed Romania’s anti-corruption agency.28
Black Cube: Intelligence for Hire
Black Cube is a private intelligence firm staffed by former intelligence operatives and closely linked to state security networks.
Its methods include:
False identities
Front companies
Direct infiltration of targets
²⁹ ³⁸
The firm has been linked to:
Surveillance of journalists
Intelligence gathering on victims of abuse
Political influence operations
³¹ ³² ³³
Internal documents reveal government contracts and dedicated departments for politically motivated operations.³⁴
It has also been connected to efforts to discredit NGOs during elections and maintains ties to former senior intelligence officials, including Mossad leadership.³⁵ ³⁶


NSO Group and Pegasus
Pegasus spyware is one of the most powerful surveillance tools ever developed commercially.
It provides access to:
Messages, emails, photos, and contacts
Location tracking
Microphone and camera activation
³⁹ ⁵⁰
It effectively turns a personal device into a surveillance system.
Pegasus has been used against:
Palestinian human rights defenders
Pro-democracy activists
Journalists across multiple countries
⁴⁰ ⁴¹
A whistleblower has alleged attempts to gain access to global mobile tracking networks.⁴²
Investigations have documented widespread use of Pegasus against activists, opposition figures, and civil society organizations.⁴³
High-profile individuals, including journalists and global figures, have also been targeted.⁴⁴ ⁴⁶

Organizations such as Amnesty International have been directly targeted as well.⁴⁷ ⁴⁸
Expansion of the Global Surveillance Market
The spyware ecosystem extends beyond a single company.
Rayzone has developed systems capable of intercepting wireless communications and accessing global telecommunications infrastructure.⁵³ ⁵⁴ ⁵⁵
Cytrox has created spyware capable of turning smartphones into full surveillance devices, similar to Pegasus.⁵⁷ ⁵⁸

The result is a growing marketplace offering governments a comprehensive surveillance toolkit.⁵⁹
Mass Surveillance Systems
These capabilities are now being deployed at scale.
Programs such as Blue Wolf have created biometric databases of entire populations, combining facial recognition with real-time monitoring systems.⁶⁰ ⁶¹ ⁶²
![A view of the entrance of the Israeli cyber company NSO Group branch in the Arava Desert in Sapir, Israel. [Amir Levy/Getty Images] A view of the entrance of the Israeli cyber company NSO Group branch in the Arava Desert in Sapir, Israel. [Amir Levy/Getty Images]](https://substackcdn.com/image/fetch/$s_!AHU_!,w_1456,c_limit,f_auto,q_auto:good,fl_progressive:steep/https%3A%2F%2Fsubstack-post-media.s3.amazonaws.com%2Fpublic%2Fimages%2Fc0639550-0958-4a39-a1dd-c7a9ab03a97a_920x613.jpeg)


Individuals can be identified and tracked before presenting identification.
This is population-level surveillance infrastructure.
At the same time, coordinated disinformation networks continue to operate across social platforms.
Meta has removed hundreds of accounts linked to coordinated campaigns, while OpenAI has reported disrupting influence operations using AI-generated political messaging.⁶⁵ ⁶⁶
These operations involve:
Fake identities
AI-generated narratives
Targeted messaging
Cross-platform amplification
A System, Not Isolated Events
Taken together, these elements form a unified structure:
Surveillance gathers information
Infiltration gains access
Disinformation shapes perception
Pressure enforces outcomes
Each component reinforces the others.
This is not fragmented activity.
It is coordinated architecture.
Why It Matters
For years, this system operated largely out of view.
That is changing.
Independent investigations are exposing operations
Researchers are mapping networks
Real-time information is bypassing traditional filters
Control depends on limiting visibility.
And visibility is increasing.
Beyond Surveillance
This is not only about spyware or intelligence operations.
It is about power.
Who controls information
controls perception
Who controls perception
controls reality
And whoever controls reality
shapes outcomes
Research Note
This article is not exhaustive.
It is a structured entry point into a much larger system.
Each referenced source can be used as a starting point for deeper investigation.








Now that you've given us a view into the capabilities of the separate ingredients of this intel surveillance and activities network, it would be interesting if you can find and describe use cases where coordinated interactions between these nodes deliver actionable insights to those using them against freedom movements. I think back to 2014 when we overthrew the elected government of Ukraine and did it somewhat with a blunt force of measures compared to what you are describing here. How have all these tools or some of these tools come together in recent events?